Dealing with Passwords
Jeff Atwood wrote a post on Coding Horror today calling out bullshit password rules. And he’s dead on. Password rules, as most sites implement them today, are not improving security. They might actually be hurting it. Even NIST agrees.
Personally, I agree with everything Jeff says. He makes several really well-researched points. But there’s one particular topic he did not mention that I want to bring to attention. Password expiration is bad (within reason). I’ve heard of (and, unfortunately, used) services that expire passwords as frequently as every 3 months. That’s just stupid. Seriously. Sometimes I don’t even visit a website that frequently! Why does it need to expire that soon? What, they store their passwords in MD5 and expect to be hacked 4 times a year? There’s no reason to expire passwords that frequently. Moreover, it’s actually harmful - what do most people do when their password expires so often they can’t remember it? They write it down on a sticky note next to their monitor. Yeah, real secure.
Really, the only time a user should need to change their password is if a website is hacked and a database is compromised. If your database hasn’t been compromised and you make your users change their password on a regular time interval, you’re providing a bad user experience with no real benefit for your users.
OK. Now that that’s off my chest, let’s talk about solutions. As a user of websites with vastly different password rules, your options are somewhat limited and they kind of suck.
July 2020 Update
I originally wrote this blog post back in 2017! I've left most of it as it was originally written because it's still accurate, but my personal views on password managers have evolved a bit since I wrote this. I'd now highly recommend using Bitwarden to manage your passwords. Read about why in my posts here and here.
What Makes a Password Secure?
Length
As it turns out, password length is probably the biggest factor in making your password more secure. Jeff’s post has all the data to back this up. Today, lots of computing power is easily available with things like Amazon EC2 and GPU parallel processing. Passwords around 8 characters in length can be cracked in minutes. The best weapon against these attacks is password length because each additional character increases the number of possible passwords exponentially. A “secure” password would be roughly 14 characters or longer.
Don’t Use Stupid Passwords
Password dumps exist on the internet. If the password you’re using exists in one of these dumps (even on someone else’s account), it’s not secure. As you might imagine, that means you can’t use simple words, “123456”, or anything like that.
Different Passwords on Different Sites
You’ve probably heard it before. Don’t use the same password for your email account that you use for your bank account. Websites get broken into all the time. If you use the same password on every website, a hack on any of the websites you visit becomes a hack on all the websites you visit. If you use a different password for each website, you limit your exposure in case any of the websites you use gets compromised.
Multi-Factor Authentication
Where it’s offered, multi-factor authentication can provide better security than a password alone. Multi-factor authentication fixes many of the problems with passwords. Accounts protected with multi-factor authentication are likely to be difficult to compromise even if the password protecting them is weak.
What are the Options
As a user, it’s hard to use good passwords. Passwords (or even password algorithms) that work on one site often won’t work on another. Websites make you change your password at random intervals. It can all be very not-user-friendly. Here are some strategies that can help.
Use Single Sign-On
Many websites are allowing their users to sign in using a Google or Facebook account. Where it’s available, I think this is a great option. I’m usually already logged in to my Google account anyway. And I trust Google to do a better job verifying my identity than most other websites. If other websites can use Google to verify my identity, that’s one less password I need to manage.
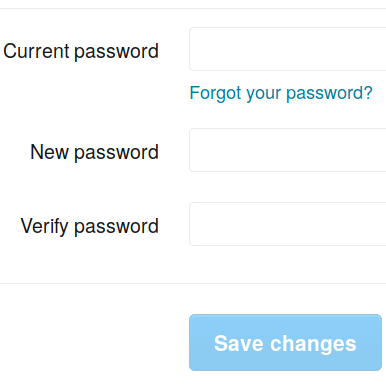
Use a Password Manager
A password manager like Bitwarden, 1Password, LastPass, Pass, or even Google can remember your passwords for you. Good ones will generate new randomized passwords for you when you sign up to new websites. Many people find this option attractive. Personally, I’m hesitant to use a password manager. Mainly because I don’t want to have to rely on it to be able to log in to all my other websites. And because I don’t like the idea of having all my passwords in one place if that service were to be hacked. But perhaps this is the way of the future - maybe I need to get over it.
(2020 Update: I did get over it. Despite all the advantages of password algorithms, which I describe below, they have many disadvantages too. They break on sites that require you to change your password frequently or that disallow special characters. I’ve been using Bitwarden for well over a year now. It’s unobtrusive, open-source, and the code’s been audited. Read more about my new thinking here and here.)
Use a Password Algorithm
I’ve been using this trick for a while on some websites. It solves the problem
of using a different password on different websites without having to remember a
large number of different passwords (and without using a password manager). It
works like this: Start with a “base” password. For example, ILikeDoughnuts.
Then, add something about the name of the website you’re logging in to. If
you’re logging into your bank, you might use BILikeDoughnutsank, combining the
works Bank and ILikeDoughnuts to form your password. Now you’ve got a
different password for each site, but you only have to remember one algorithm.
Wrapping Up
Unfortunately, passwords are in some ways a necessary evil. Something that isn’t ideal but something we have to deal with. Understanding the different approaches to dealing with them and the trade-offs between the approaches is really important.
What password strategies do you use? How can software developers make the login experience more user-friendly?
About the Author

👋 Hi, I'm Mike! I'm a husband, I'm a father, and I'm a staff software engineer at Strava. I use Ubuntu Linux daily at work and at home. And I enjoy writing about Linux, open source, programming, 3D printing, tech, and other random topics. I'd love to have you follow me on X or LinkedIn to show your support and see when I write new content!
I run this blog in my spare time. There's no need to pay to access any of the content on this site, but if you find my content useful and would like to show your support, buying me a coffee is a small gesture to let me know what you like and encourage me to write more great content!
You can also support me by visiting LinuxLaptopPrices.com, a website I run as a side project.
Related Posts
- How I Manage Passwords with KeePass 25 Mar 2017
- Dotfiles Secrets in Chezmoi, Without Password Headaches 31 Jan 2026
- Testing is Hard 28 Jan 2017